(BackTrack 5 R1: Lesson 11)
{ How to Enable Tamper Data }
| Section 0. Background Information |
- What is tamper data?
- Tamper Data is a Firefox Extension which gives you the power to view, record and modify outgoing HTTP/HTTPS requests (headers and post parameters)
- Pre-Requisite Lab
-
BackTrack: Lesson 1: Installing BackTrack 5 R1
- Note: This is not absolutely necessary, but if you are a computer security student or professional, you should have a BackTrack VM.
-
BackTrack: Lesson 1: Installing BackTrack 5 R1
-
Lab
Notes
- In this lab we will do the following:
- We will enable Tamper Data in Firefox on BackTrack 5R1.
- In this lab we will do the following:
- Legal Disclaimer
- As a condition of your use of this Web site, you warrant to computersecuritystudent.com that you will not use this Web site for any purpose that is unlawful or that is prohibited by these terms, conditions, and notices.
- In accordance with UCC § 2-316, this product is provided with "no warranties, either express or implied." The information contained is provided "as-is", with "no guarantee of merchantability."
- In addition, this is a teaching website that does not condone malicious behavior of any kind.
- You are on notice, that continuing and/or using this lab outside your "own" test environment is considered malicious and is against the law.
- © 2013 No content replication of any kind is allowed without express written permission.
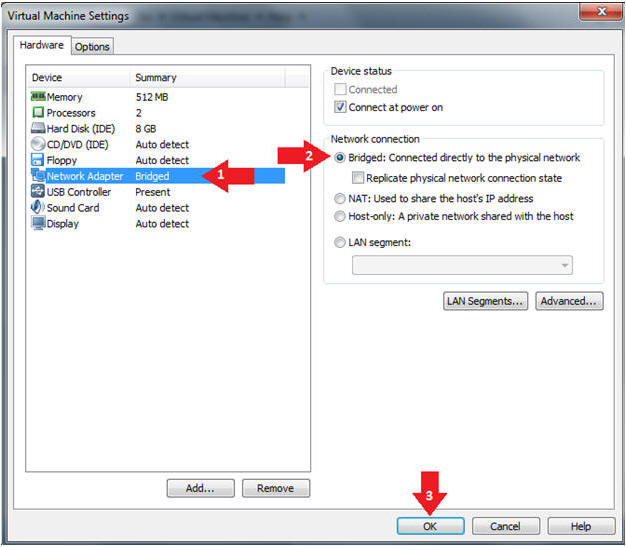
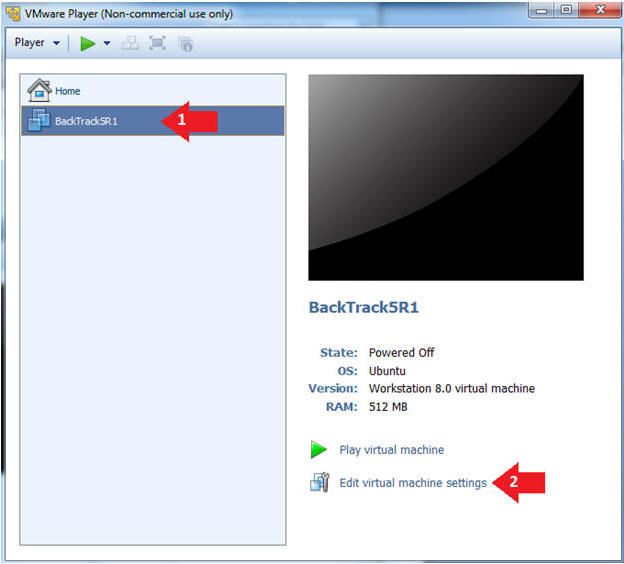
| Section 1: Configure BackTrack Virtual Machine Settings |
- Edit the BackTrack5R1 VM
- Instructions:
- Select BackTrack5R1 VM
- Click Edit virtual machine settings
- Instructions:
- Edit Virtual Machine Settings
- Instructions:
- Click on Network Adapter
- Click on the Bridged Radio button
- Click on the OK Button
- Instructions:
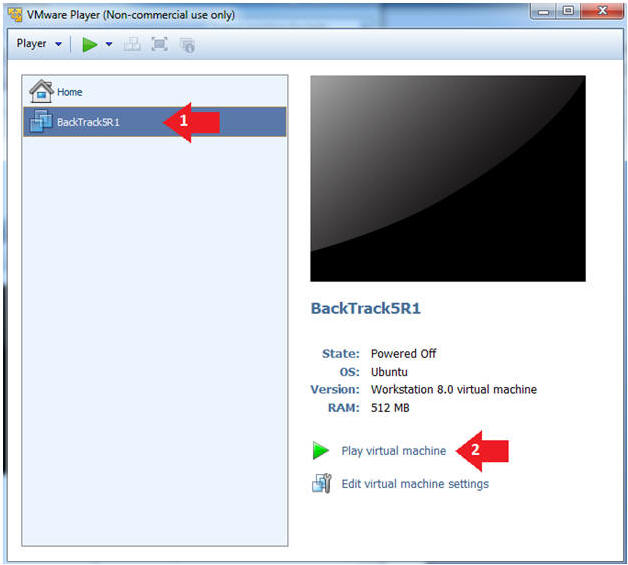
| Section 2: Play and Login to BackTrack |
- Play the BackTrack5R1 VM
- Instructions:
- Click on the BackTrack5R1 VM
- Click on Play virtual machine
- Instructions:
- Login to BackTrack
- Instructions:
- Login: root
- Password: toor or <whatever you changed it to>.
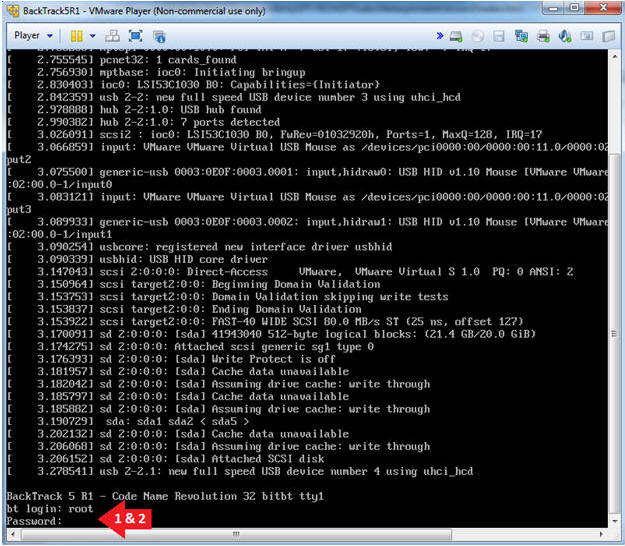
- Instructions:
- Bring up the GNOME
- Instructions:
- Type startx
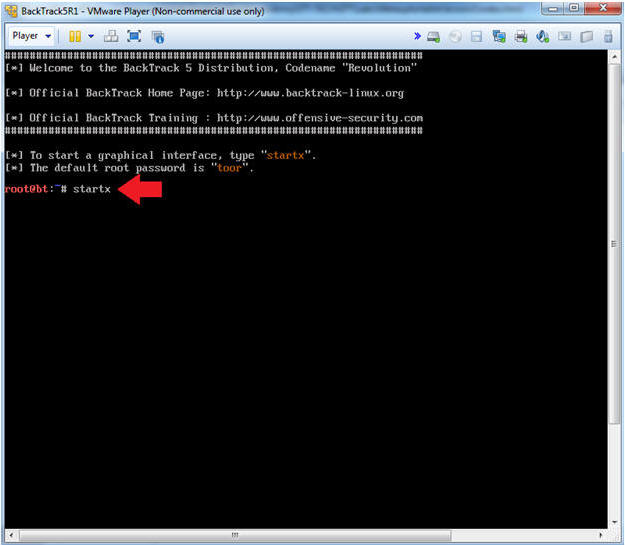
- Instructions:
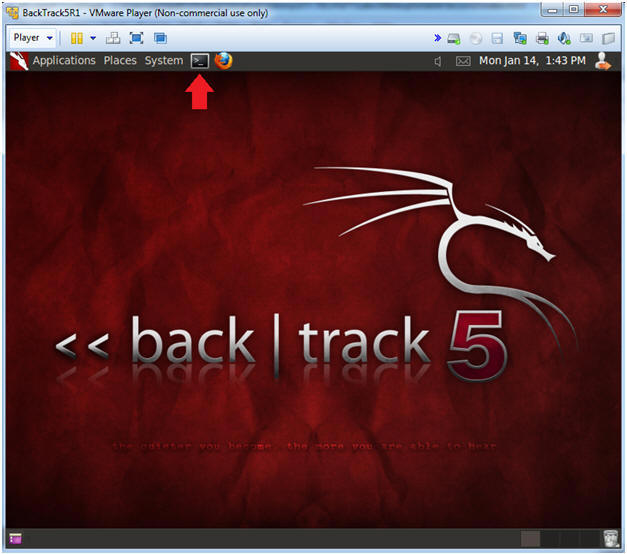
| Section 3: Open Console Terminal and Retrieve IP Address |
- On BackTrack, Start up a terminal window
- Instructions:
- Click on the Terminal Window
- Instructions:
- Obtain the IP Address
- Instructions:
- ifconfig -a
- Note(FYI):
- My IP address 192.168.1.109.
- In your case, it will probably be different.
- This is the machine that will be use to attack the victim machine (Metasploitable).
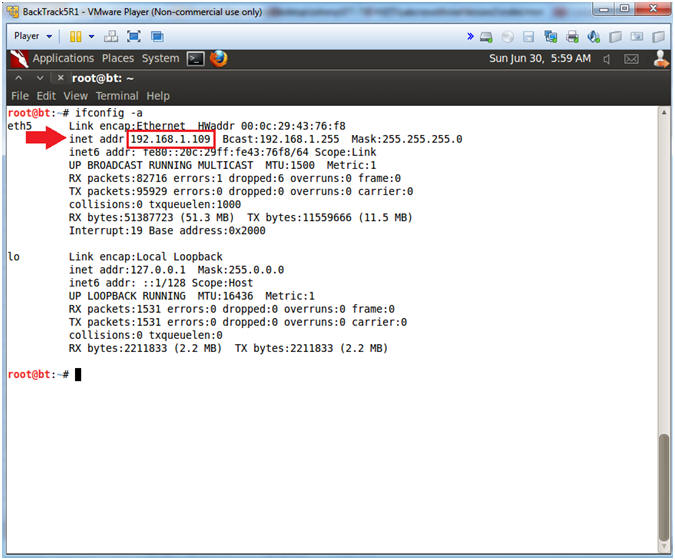
- Instructions:
| Section 4: Enable Tamper Data |
- Start Firefox
- Instructions:
- Click on Firefox

- Instructions:
- Select Add-ons
- Instructions:
- Tools --> Add-ons
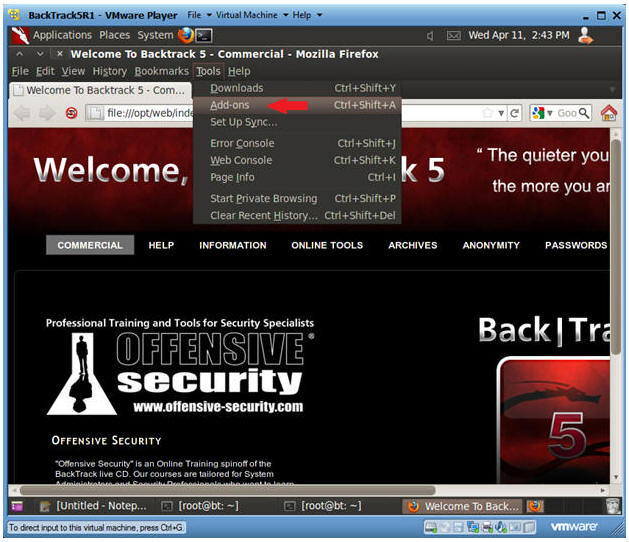
- Instructions:
- Enable Tamper Data
- Instructions:
- Click on Extensions
- Click on Tamper Data Enable Button
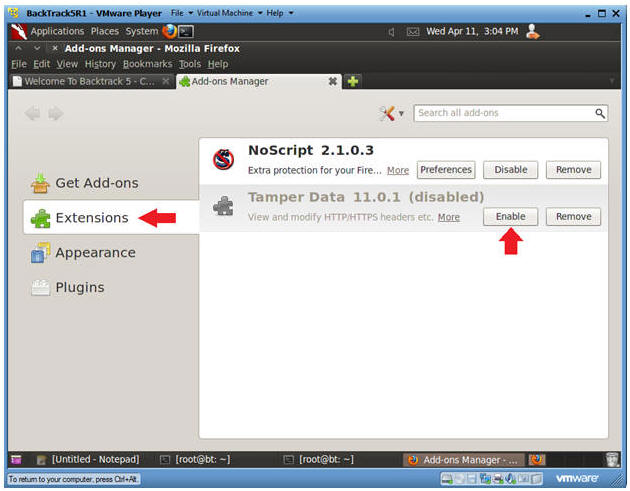
- Instructions:
- Restart Firefox
- Instructions:
- Click Restart Now (See Picture)
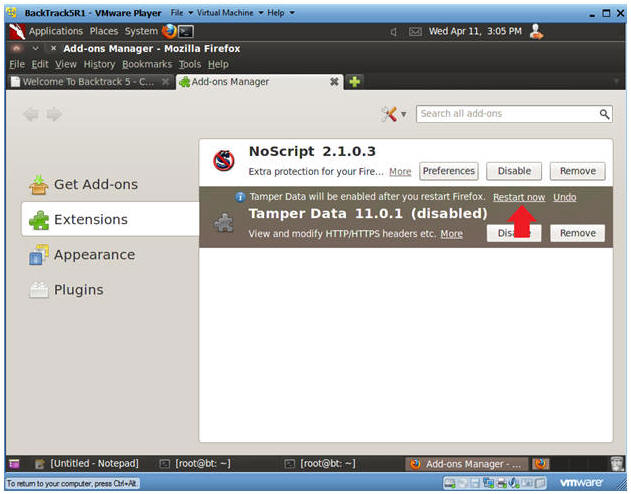
- Instructions:
| Section 15: Proof of Lab |
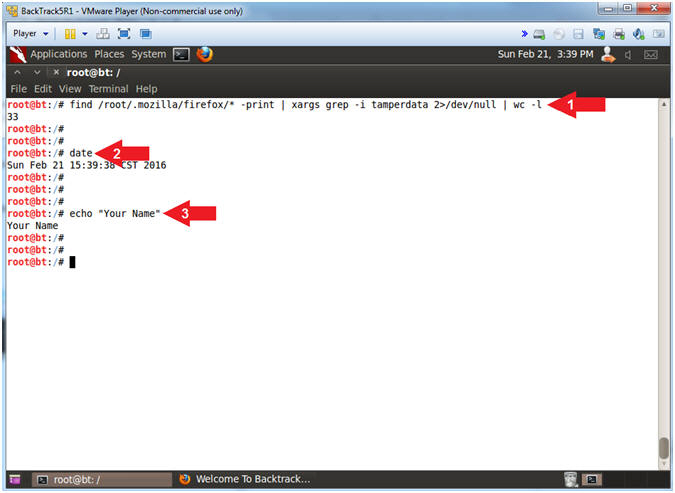
- Proof of Lab, (On a BackTrack Terminal)
- Instructions:
- find /root/.mozilla/firefox/* -print |
xargs grep -i tamperdata 2>/dev/null | wc -l
- find /root/.mozilla/firefox/*, Search the (/root/.mozilla/firefox/) path
- xargs grep -i tamperdata, Search for the string (tamperdata) and ignore case (grep -i).
- 2>/dev/null, Send standard error into a black hole .
- wc -l, Count the number of results. Where (-l) is a lowercase L.
- date
- echo "Your Name"
- Replace the string "Your Name" with your actual name.
- e.g., echo "John Gray"
- find /root/.mozilla/firefox/* -print |
xargs grep -i tamperdata 2>/dev/null | wc -l
-
Proof of Lab Instructions:
- Do a PrtScn
- Paste into a word document
- Upload to Moodle
-
- Instructions: