(CentOS 6.6: Lesson 7)
{ Installing, Configuring and Securing SSHD }
| Section 0. Background Information |
- What is Secure Shell?
- Secure Shell (SSH) is a network protocol for secure data communication, remote shell services or command execution and other secure network services between two networked computers that it connects via a secure channel over an insecure network.
- The protocol specification distinguishes two major versions that are referred to as SSH-1 and SSH-2.
- The best-known application of the protocol is for access to shell accounts on Unix-like operating systems.
- It was designed as a replacement for Telnet and other insecure remote shell protocols such as the Berkeley rsh and rexec protocols, which send information, notably passwords, in plaintext, rendering them susceptible to interception and disclosure using packet analysis.
- The encryption used by SSH is intended to provide confidentiality and integrity of data over an unsecured network, such as the Internet.
- What Is YUM?:
- The Yellowdog Updater, Modified (YUM) is an open-source command-line package-management utility for RPM-compatible Linux operating systems and has been released under the GNU General Public License. YUM has been adopted by Red Hat Enterprise Linux, Fedora, CentOS, and many other RPM-based Linux distributions, including Yellow Dog Linux itself, where it has replaced the original YUP utility
- Pre-Requisite Lab
-
Lab
Notes
- In this lab we will do the following:
- Install openssh-server.
- Configure openssh-server.
- Test openssh-server.
- In this lab we will do the following:
- Legal Disclaimer
- As a condition of your use of this Web site, you warrant to computersecuritystudent.com that you will not use this Web site for any purpose that is unlawful or that is prohibited by these terms, conditions, and notices.
- In accordance with UCC § 2-316, this product is provided with "no warranties, either express or implied." The information contained is provided "as-is", with "no guarantee of merchantability."
- In addition, this is a teaching website that does not condone malicious behavior of any kind.
- You are on notice, that continuing and/or using this lab outside your "own" test environment is considered malicious and is against the law.
- © 2015 No content replication of any kind is allowed without express written permission.
| Section 1. Configure CentOS-6.6 Virtual Machine Settings |
- Open Your VMware Player
- Instructions:
- On Your Host Computer, Go To
- Start --> All Program --> VMWare --> VMWare Player
- Instructions:
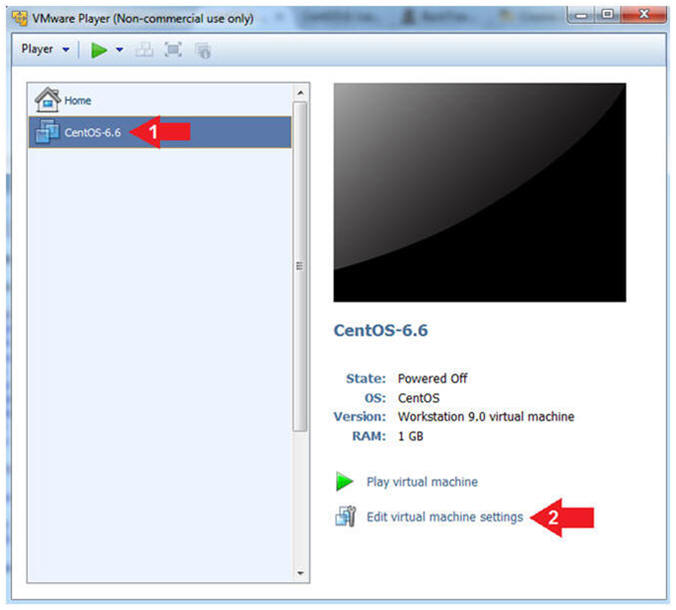
- Edit CentOS-6.6 Virtual Machine Settings
- Instructions:
- Highlight CentOS-6.6
- Click Edit virtual machine settings
- Instructions:
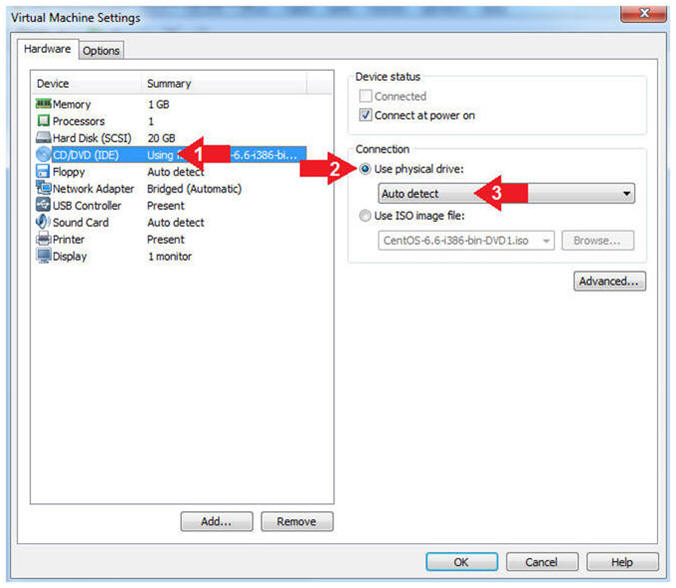
- Auto Detect Hard Drive
- Instructions:
- Click on CD/DVD(IDE)
- Click the Use physical drive: radio button
- Make sure Auto detect is selected
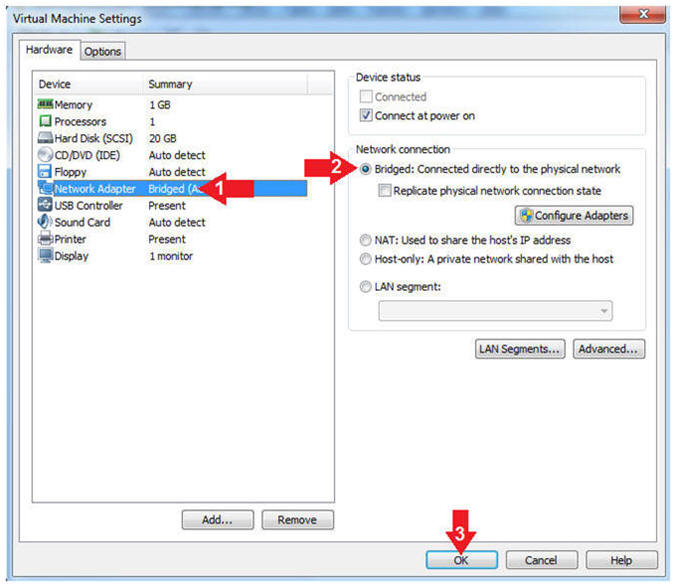
- Instructions:
- Edit Network Adapter
- Instructions:
- Highlight Network Adapter
- Select Bridged
- Click the OK Button
- Instructions:
| Section 2. Play Virtual Machine |
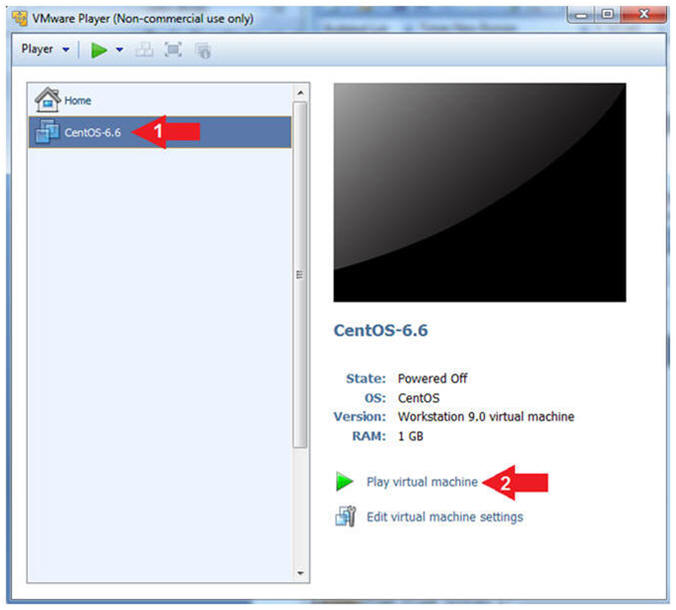
- Start the CentOS-6.6 VM
- Instructions:
- Click on the CentOS-6.6 VM
- Click on Play virtual machine
-
- Instructions:
| Section 3. Login to CentOS |
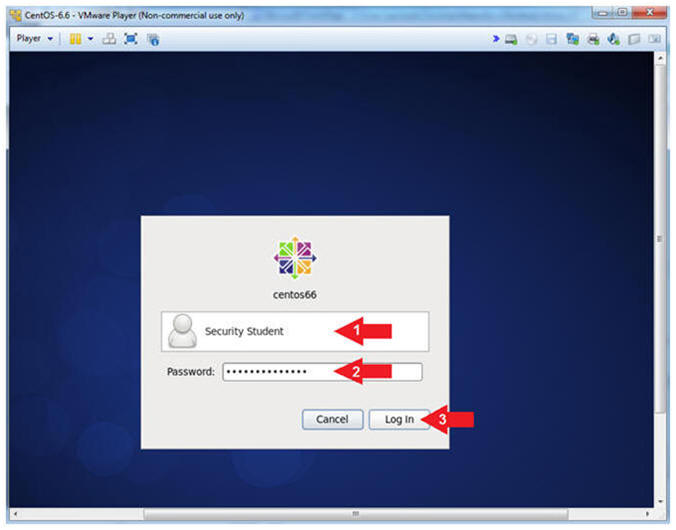
- Login to CentOS
- Note(FYI):
- Until you click the user, in this case Security Student, the Password field will not be displayed.
- Instructions:
- Click on Security Student
- This will display the password text box.
- Supply its' password
- Click the Log In Button
- Click on Security Student
- Note(FYI):
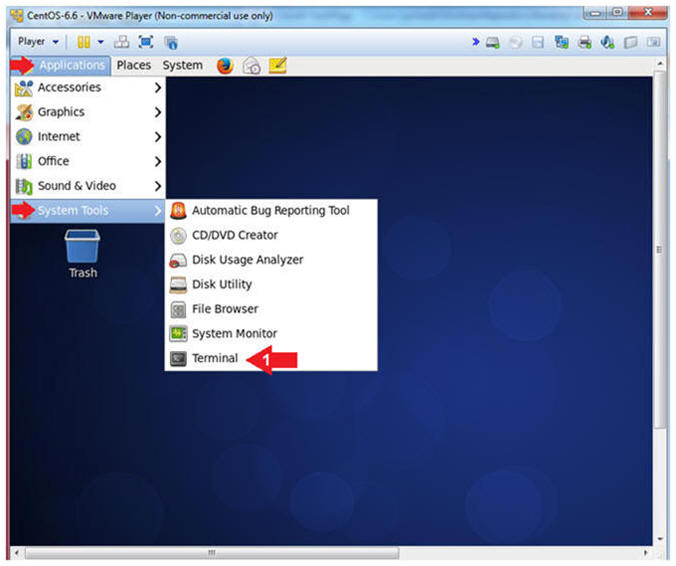
- Open a Terminal
- Instructions:
- Applications --> System Tools --> Terminal
- Instructions:
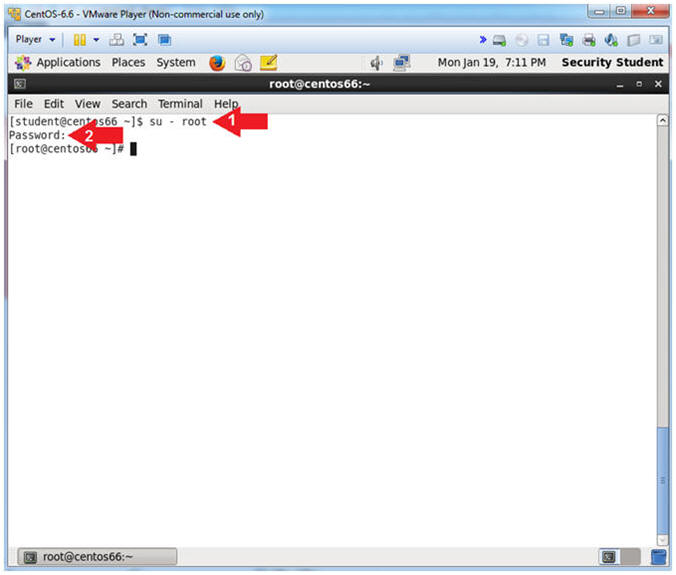
- Switch User to root
- Instruction:
- su - root
- Supply the Root Password
- Notes (FYI):
- su - root, this command allows the user student to switch user to user root, provided the root password can be supplied.
- Instruction:
- Get IP Address
- Instructions:
- ifconfig -a
- Notes (FYI):
- As indicated below, my IP address is
192.168.1.101 for Network Interface eth1.
- Please record your IP address
- The Local Loopback Address is 127.0.0.1
for Network Interface lo.
- The loopback device is a special, virtual network interface that your computer uses to communicate with itself. When the network or wifi is disconnected the loopback exists so applications running on your computer can always connect to servers on the same machine.
- As indicated below, my IP address is
192.168.1.101 for Network Interface eth1.
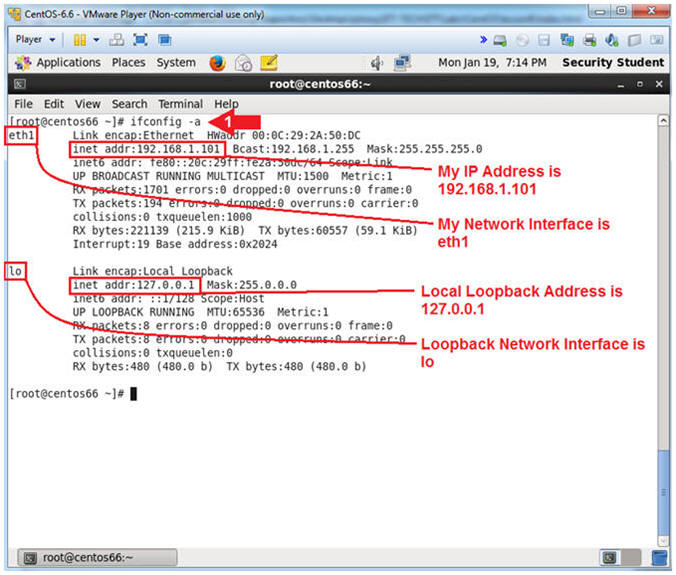
- Instructions:
| Section 4. Installing openssh |
- Check to see if openssh-server is installed.
- Instruction:
- rpm -qa | grep "openssh-server"
- rpm -qi
openssh-server-5.3p1-104.el6.i686
- Paste the packate name results after the rpm -qi
- Note(FYI):
- rpm - RPM Package Manager
- q = query
- a = all packages
- i = Display package information, including name, version, and description.
- grep = Search for string "open-server"
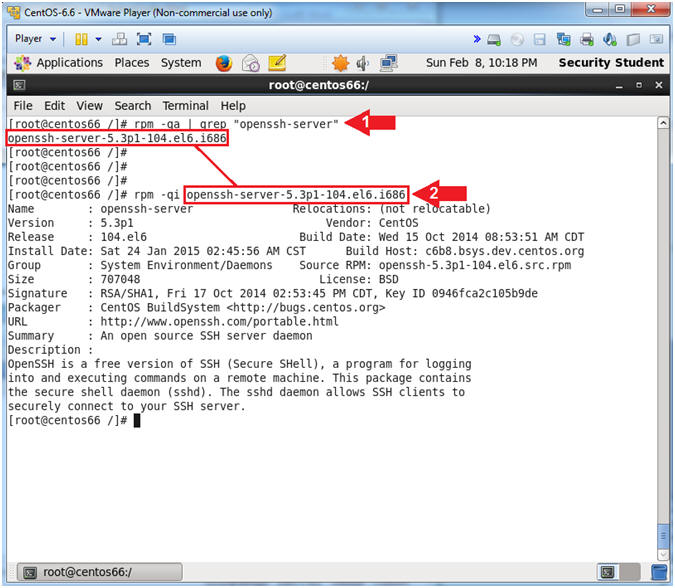
- Instruction:
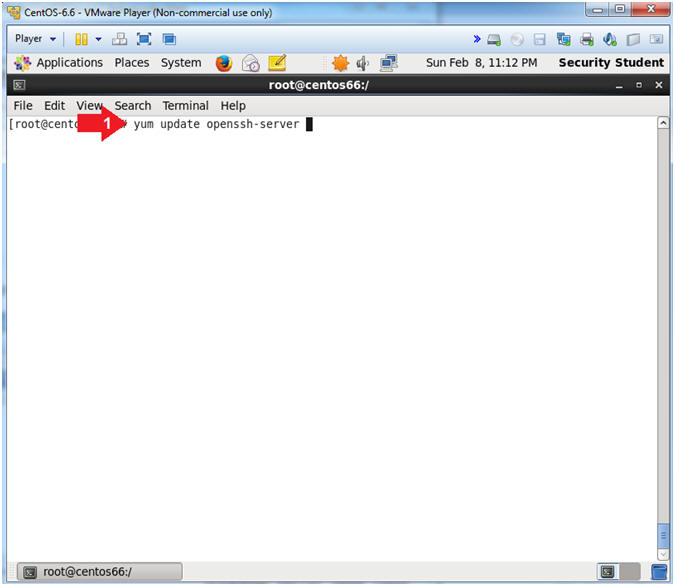
- Let's update openssh-server
- Instruction:
- yum update openssh-server
- Note(FYI):
- If openssh-server was not found, then your
command would be:
- yum install openssh-server
- It's always a good idea to make sure you have the latest update for ssh.
- If openssh-server was not found, then your
command would be:
- Instruction:
- Install openssh-server.
- Instructions:
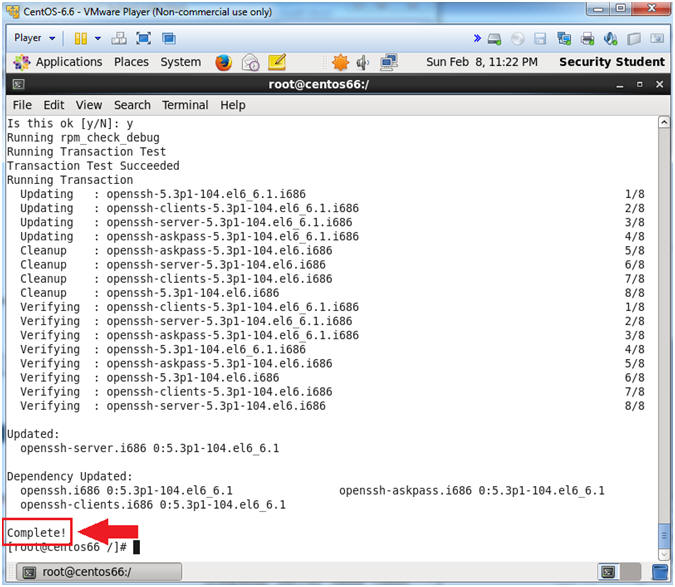
- Is this ok [y/N]: y
- Is this ok [y/N]: y
- Note(FYI):
- YUM reports that the latest update is 5.3p1-104.el6_6.1.
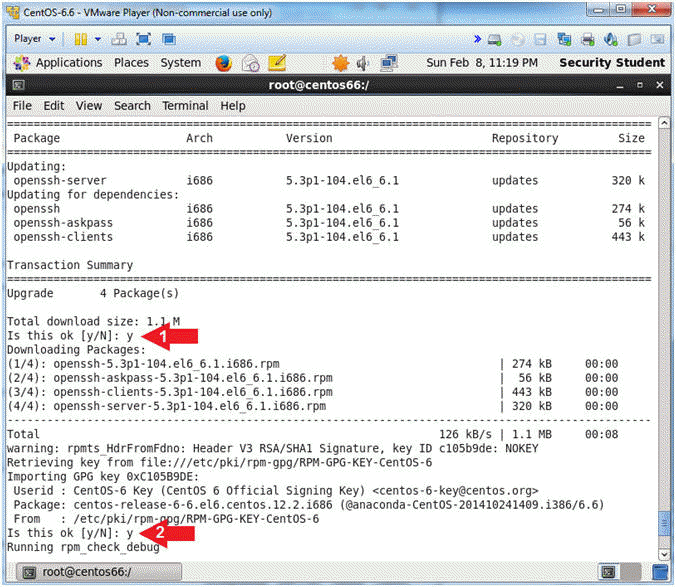
- Instructions:
- Installation Analysis
- Note(FYI):
- You will see that the below packages have been updated followed by the "Complete!" message.
- Note(FYI):
| Section 5. Starting openssh |
- Check to see if sshd is running.
- Instructions:
- service sshd stop
- ps -eaf | grep sshd | grep -v grep | wc -l
- Note(FYI):
- service sshd stop
- I stopped the sshd process on purpose to show you how to use the "ps" command.
- ps -eaf | grep sshd | grep -v grep | wc -l
- ps -eaf = List all running processes
- grep sshd = search for sshd is the process list.
- grep -v grep = ignore the grep process in the process list.
- wc -l = count how many times sshd is listed.
- As a result, "0" line were counted, which means sshd is not running.
- service sshd stop
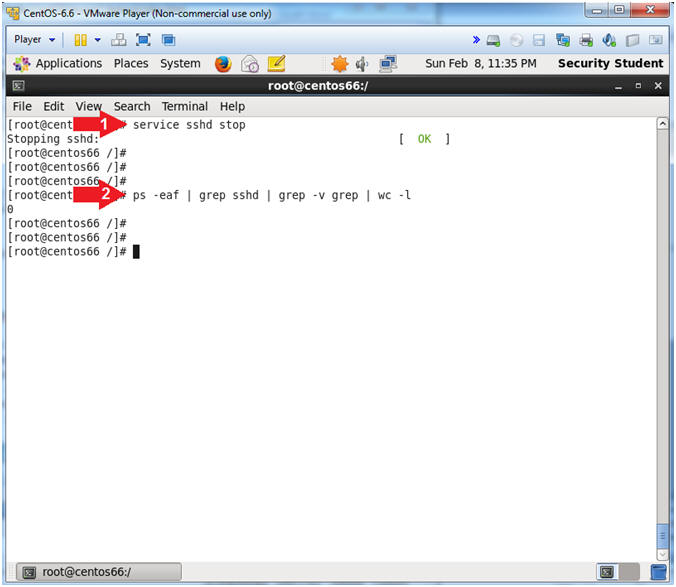
- Instructions:
- Investigating Startup and Kill Scripts
- Instructions:
- ls -l /etc/rc[0-6].d/* | grep ssh
- Note(FYI):
- The /etc directory contains rc (run command) scripts.
- rc scripts contain Startup (e.g., S55sshd) and Kill (e.g., K25sshd) scripts.
- The rc scripts dictate which scripts get started or killed during change in run-level.
- Run level Explanations
- 0, Halt, Shuts down the system.
- 1, Single-user Mode, Mode for administrative tasks.
- 2, Multi-user Mode, Does not configure network interfaces and does not export networks services.
- 3, Multi-user Mode with Networking, Starts the system normally.
- 4, Not used/User-definable, For special purposes.
- 5, Start the system normally with appropriate display manager. ( with GUI ), Same as runlevel 3 + display manager.
- 6, Reboot, Reboots the system.
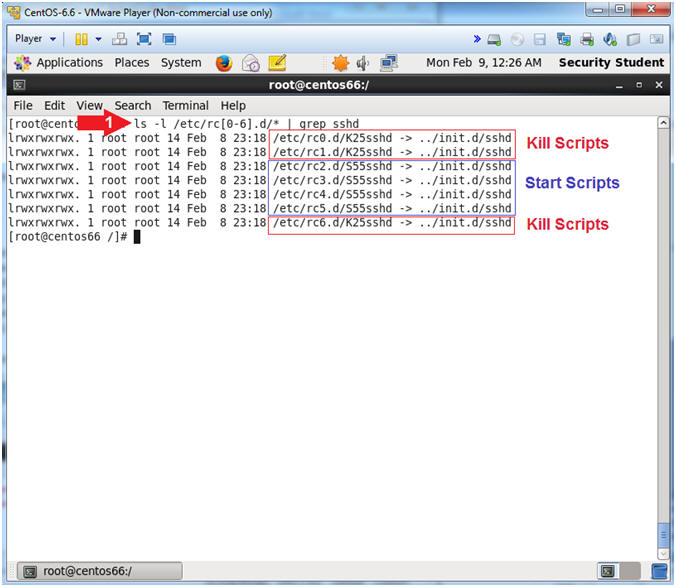
- Instructions:
- chkconfig relates to rc scripts
- Instruction:
- chkconfig --list | grep ssh
- Note(FYI):
- chkconfig - updates and queries runlevel information for system services.
- chkconfig has five distinct functions:
adding new services for management, removing services from
management,
listing the current startup information for services, changing the startup information for services, and checking
the startup state of a particular service. - Notice that run-levels 2,3,4,5 are all on and they have corresponding Start Up Scripts.
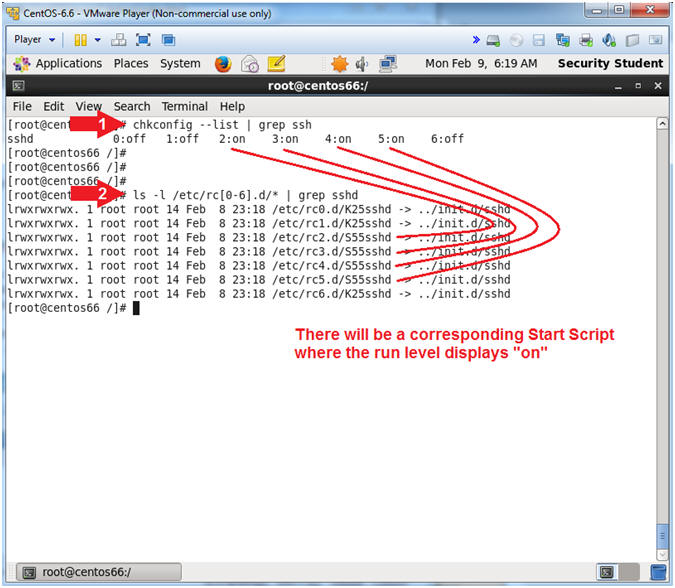
- Instruction:
- Create Startup scripts for sshd
- Instructions:
- chkconfig sshd --level 2345 on
- chkconfig --list | grep ssh
- Note(FYI):
- Create SSHD start up scripts for run-level 2, 3, 4 and 5.
- Notice that chkconfig now shows that a startup script exists for run levels 2, 3, 4 and 5.
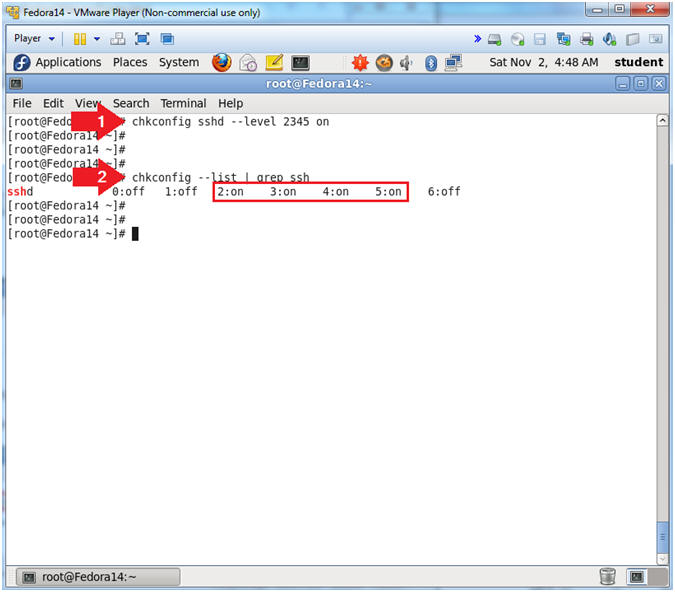
- Instructions:
- Verify Startup scripts have been created using
the find command.
- Instructions:
- chkconfig sshd --level 2345 off
- chkconfig --list | grep ssh
- ls -l /etc/rc[0-6].d/* | grep sshd
- chkconfig sshd --level 2345 off
- ls -l /etc/rc[0-6].d/* | grep sshd
- Note(FYI):
- Turn off all the sshd Start Up Scripts for run-levels 2, 3, 4 and 5.
- Verify with chkconfig that the sshd Start Up Scripts for run-levels 2, 3, 4 and 5 are off.
- Verify with the "ls -l" command that the sshd Start Up Scripts for run-levels 2, 3, 4 and 5 are off.
- Turn on all the sshd Start Up Scripts for run-levels 2, 3, 4 and 5.
- Verify with chkconfig that the sshd Start Up Scripts for run-levels 2, 3, 4 and 5 are on.
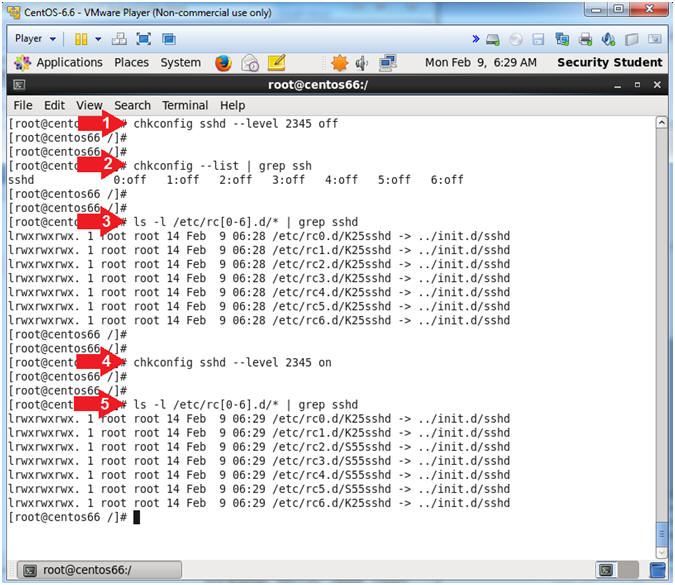
- Instructions:
- Let's start up the sshd daemon.
- Instruction:
- service sshd start
- ps -eaf | grep ssh | grep -v grep
- Note(FYI):
- Start the sshd listening daemon/service.
- Display all (ps -eaf | grep ssh) ssh process and ignore (grep -v grep) the actual grep process.
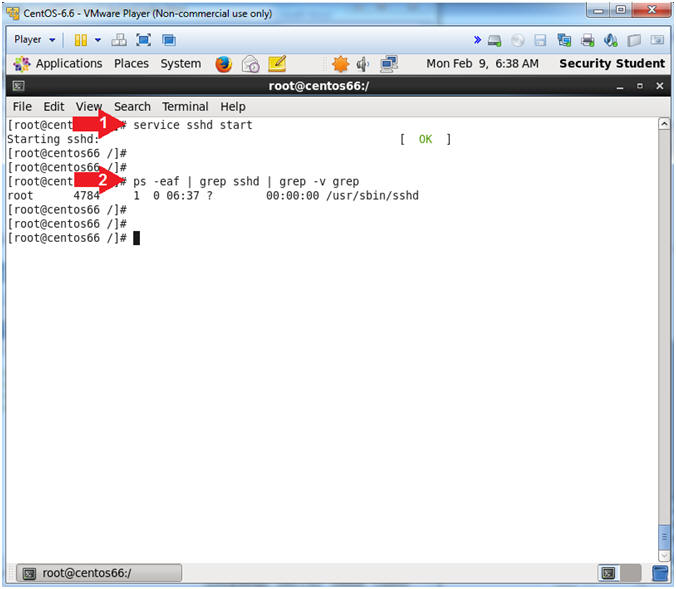
- Instruction:
| Section 6. Secure openssh |
- Make a sshd_config backup file.
- Instruction:
- cd /etc/ssh
- cp sshd_config ssh_config.BKP
- ls -l sshd_config*
- Note(FYI):
- Change directory to /etc/ssh. This is where the ssh configuration files exist.
- Make a backup copy, so if you mess something up, you can revert to the original file.
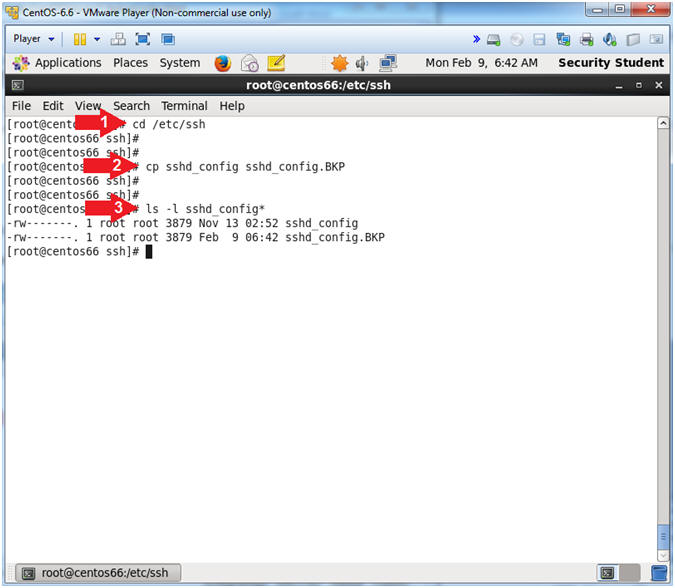
- Instruction:
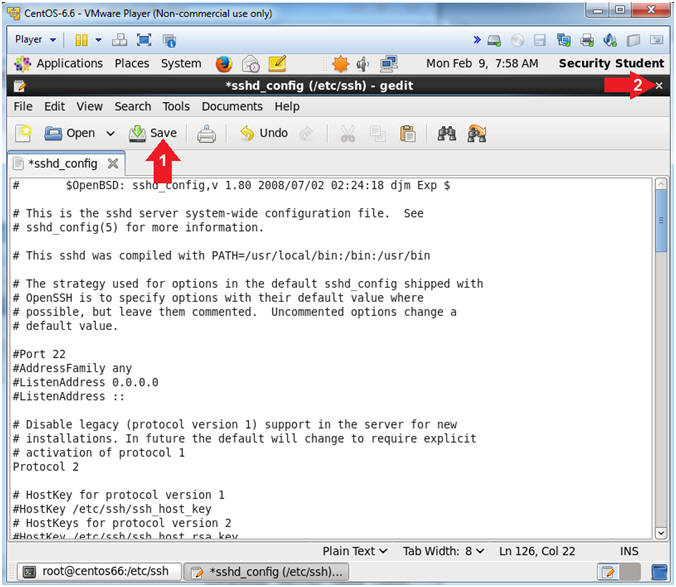
- Open sshd_config
- Instruction:
- gedit sshd_config 2>/dev/null &
- Note(FYI):
- gedit, is a text editor for the GNOME desktop environment.
- sshd_config is the name of the file.
- 2>/dev/null, send any gedit error messages into a black hole, as in don't display them.
- &, means put the process of opening gedit sshd_config in the background.
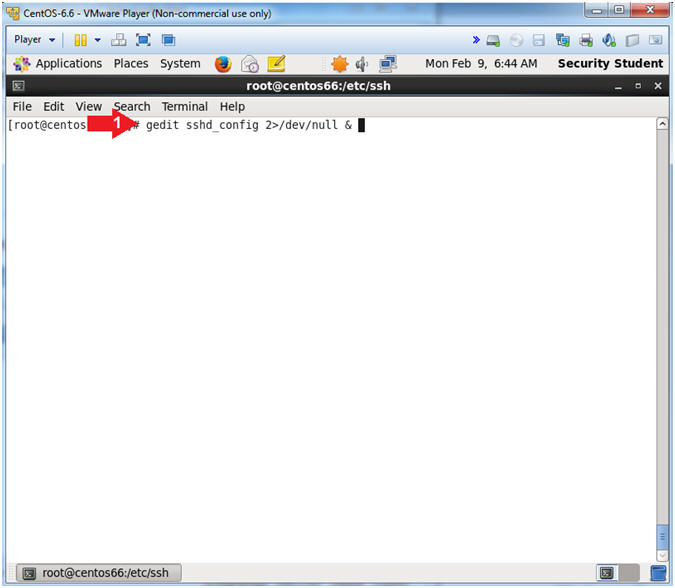
- Instruction:
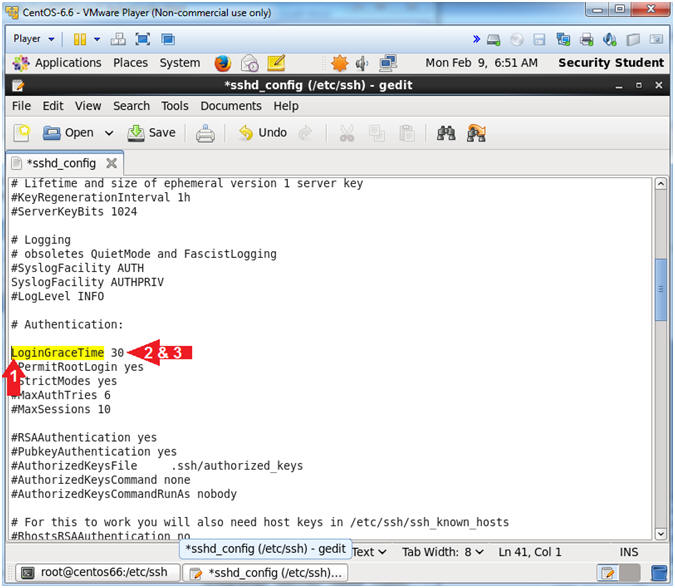
- Find LoginGraceTime
- Instructions:
- Arrow down to "#LoginGraceTime 2m"
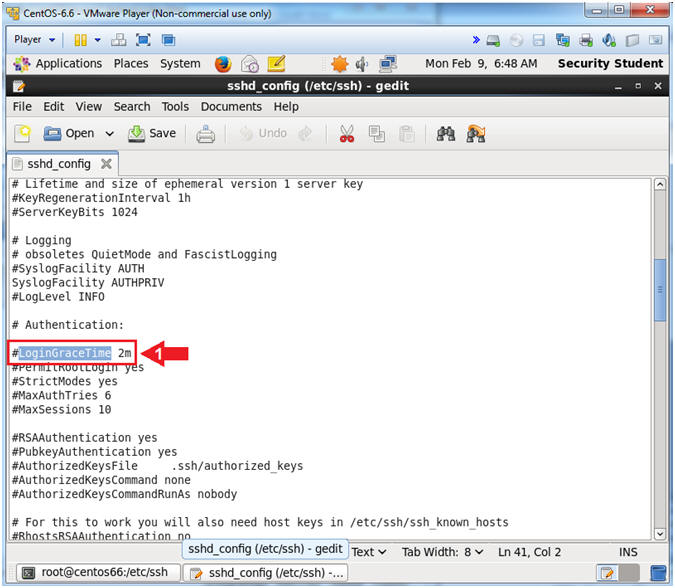
- Instructions:
- Reduce Unauthenticated Disconnect Time
- Instructions:
- Delete the "#" character that proceeds "#LoginGraceTime 2m".
- Change 2m to 30.
- Note(FYI):
- The default of 2 minutes is too much time to stay open for an unauthenticated connection attempt. So, we will reduce the amount of time to remain open from 2 minutes to 30 seconds.
- Instructions:
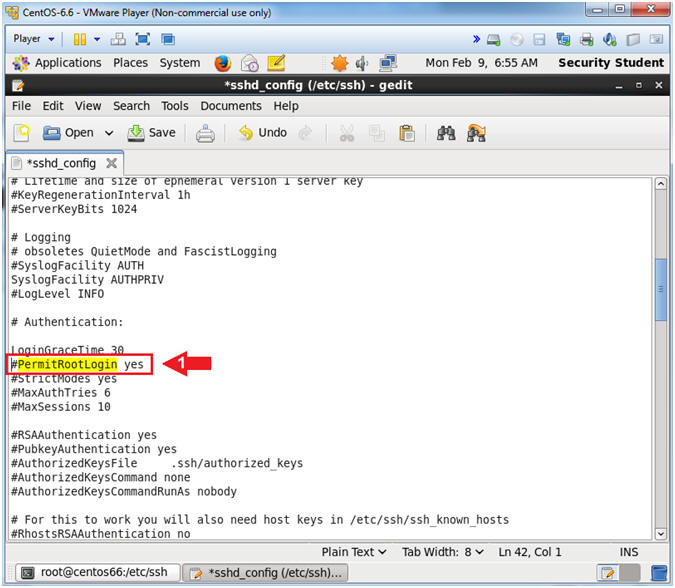
- Find
"#PermitRootLogin yes"
- Instruction:
- Arrow down to "#PermitRootLogin yes"
- Instruction:
- Configure and Disable PermitRootLogin
- Instructions:
- Delete the "#" character that proceeds PermitRootLogin.
- Replace "yes" with a "no" and that follows PermitRootLogin.
- Note(FYI):
- This will disabled the ability for somebody to login as root.
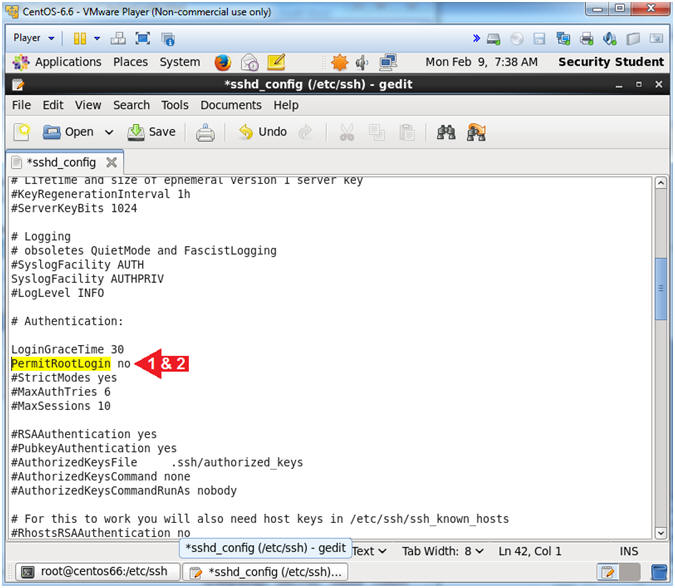
- Instructions:
- Configure PAM authentication
- Instructions:
- Arrow down until you get to the line "#UsePAM no"
- Verify "UsePAM yes" exists under the line "#UsePAM no"
- Note(FYI):
- If the line "UsePAM yes" already exists, then you are not required to do anything. If it does NOT exist, then add it.
- Basically, we need to verify that there is a line stating "UsePAM yes".
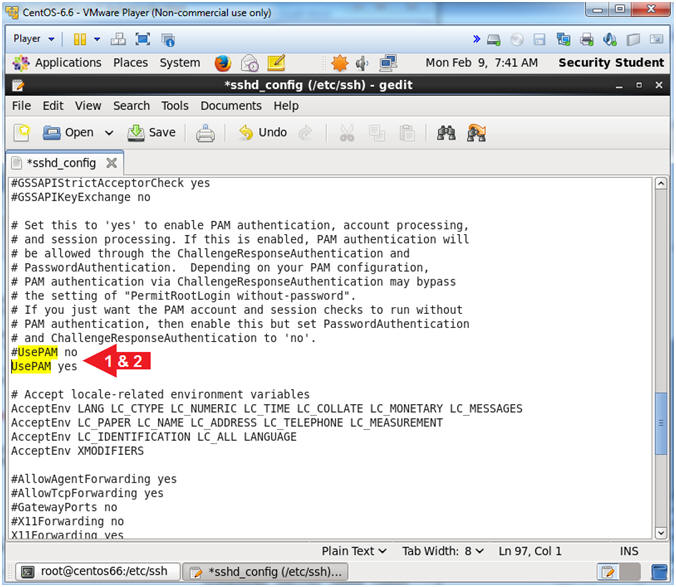
- Instructions:
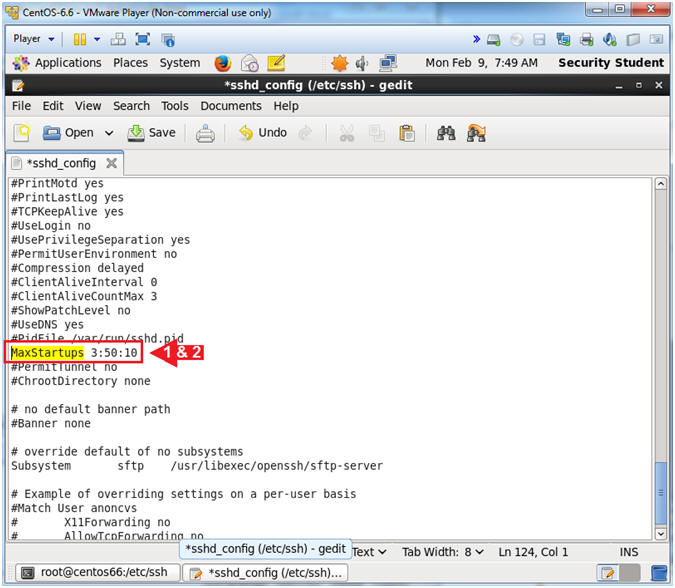
- Find "#MaxStartups"
- Instructions:
- Arrow down until you get to the line "#MaxStartups 10:30:100"
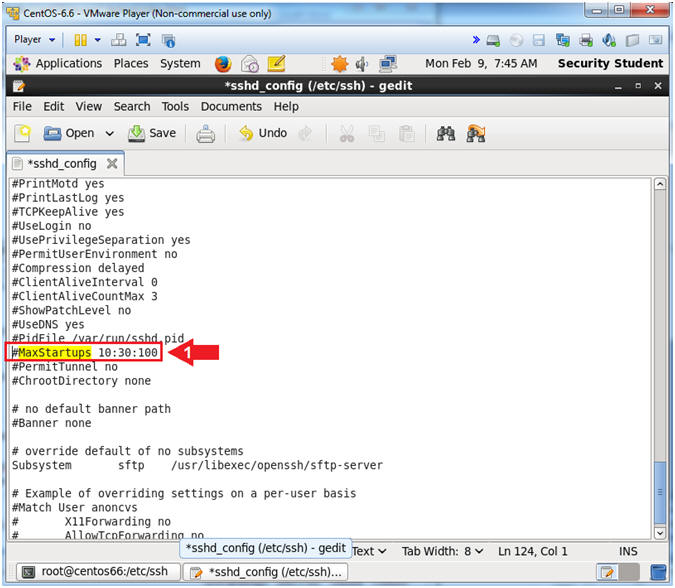
- Instructions:
- Limit the maximum number of unauthenticated
connections that the ssh server will handle at the same time.
- Instructions:
- Remove the "#" character that proceeds "#MaxStartups 10:30:100".
- Change 10:30:100 to 3:50:10
- Note(FYI):
- The smaller the number is the harder it is for attackers to make parallel, coordinated brute force attempts with multiple connections.
- 3: Allow 3 unauthenticated connections before dropping connections.
- 50: There is a 50 percentage chance of dropping connections once we reach 3 connections.
- 10: max number of connections at which we start dropping everything
- Instructions:
- Save and Close sshd_config
- Instructions:
- Click Save
- Click the "X" to Close
- Instructions:
- Restart the sshd daemon.
- Instructions:
- service sshd restart
- ps -eaf | grep sshd | grep -v grep
- Note(FYI):
- When ever you make a change to the sshd_config file, you will need to restart the sshd daemon in order for the changes to take affect.
- Verify the sshd daemon/service is running.
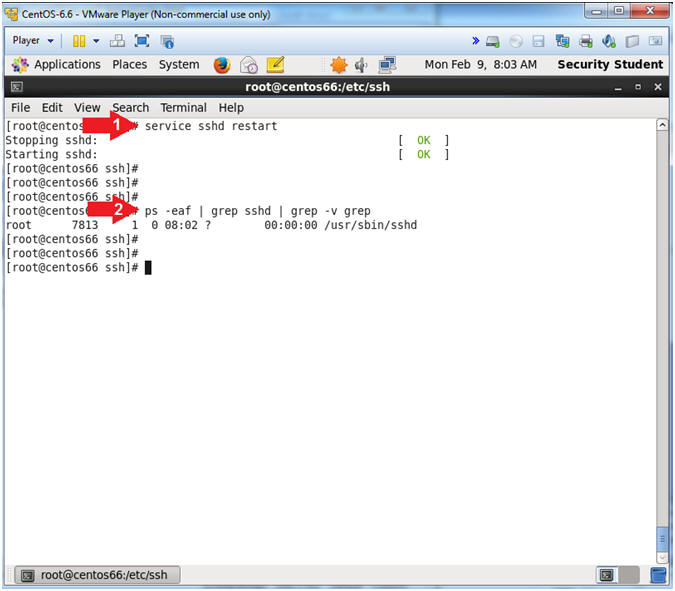
- Instructions:
| Section 7. Configure Firewall |
- Open the Firewall
- Instructions:
- System --> Administration --> Firewall
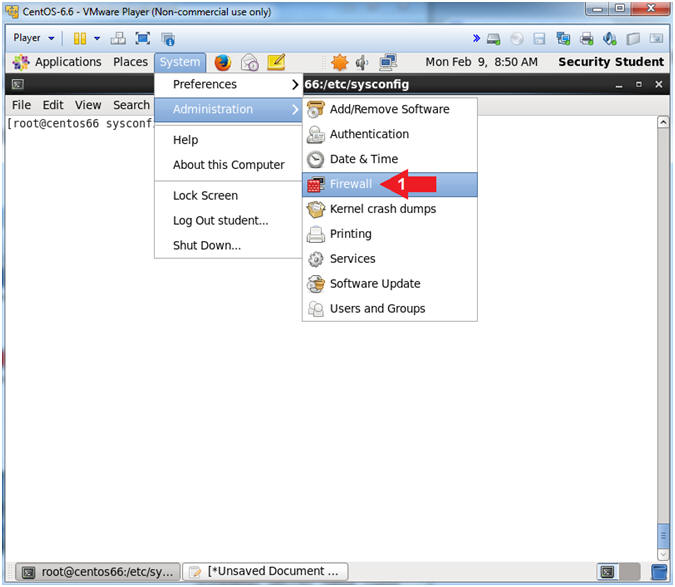
- Instructions:
- Firewall Configuration Startup Message
- Instructions:
- Click the Close Button
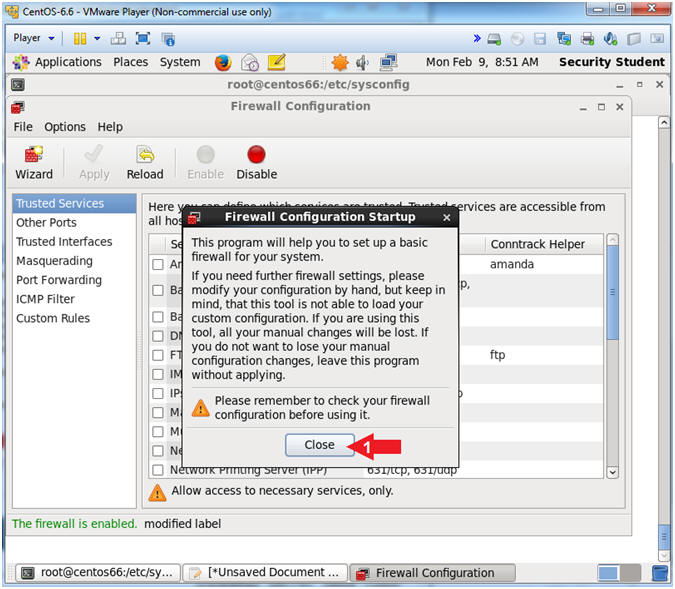
- Instructions:
- Enter the root password
- Instructions:
- Supply the root password
- Click the Authenticate Button
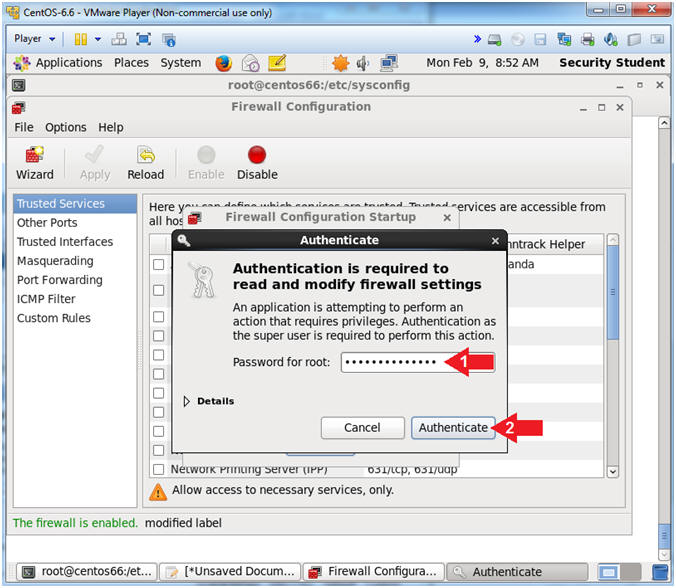
- Instructions:
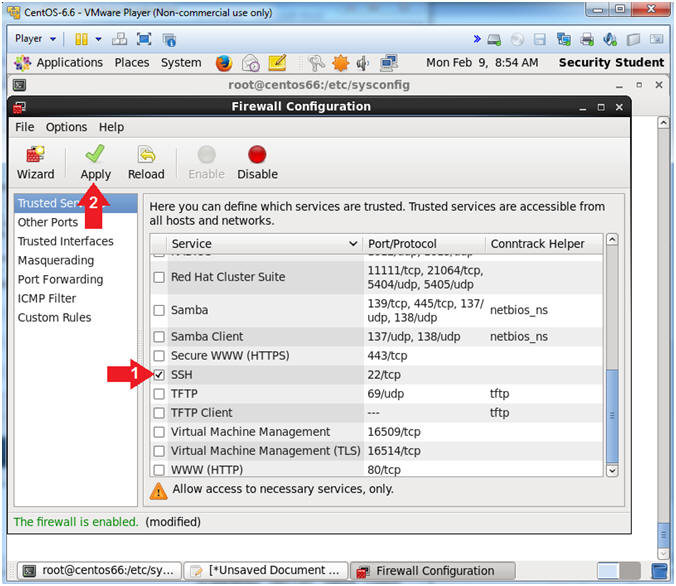
- Enable SSH
- Instructions:
- Un-Check and Check the SSH checkbox
- If this box is already checked, uncheck and recheck it.
- Click on the Apply Green Checkmark
- Un-Check and Check the SSH checkbox
- Instructions:
- system-config-firewall message
- Instructions:
- Click the Yes button
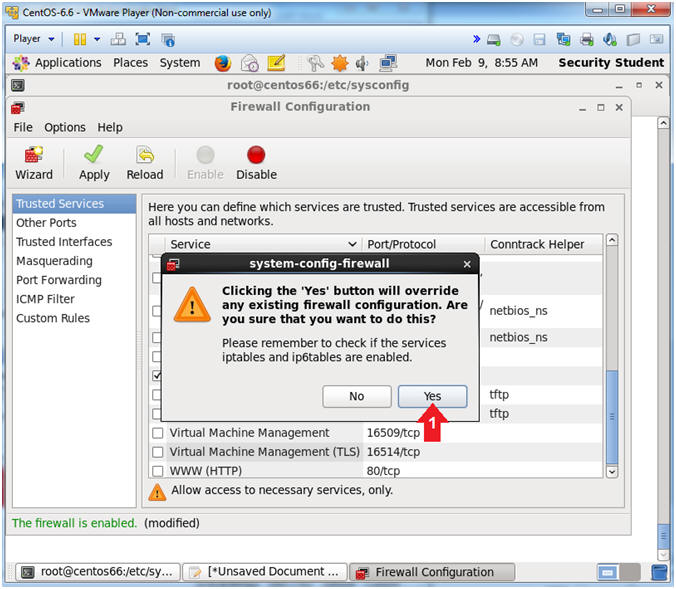
- Instructions:
- Reload Firewall
- Instructions:
- Click Reload
- Click the X to close
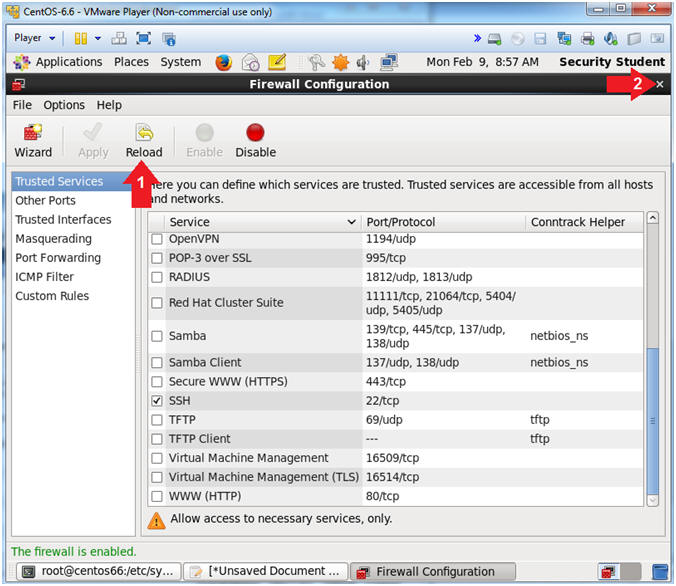
- Instructions:
| Section 8. Test sshd to not allow root to login |
- Test sshd to not allow root to login
- Instructions:
- ssh root@localhost
- Are you sure you want to continue connecting (yes/no)? yes
- Supply root password
- Supply root password again
- Supply root password again
- Note(FYI):
- If you get prompted for an RSA key fingerprint, then answer "yes"
- Notice that even though you are typing the correct root password you are not able to login.
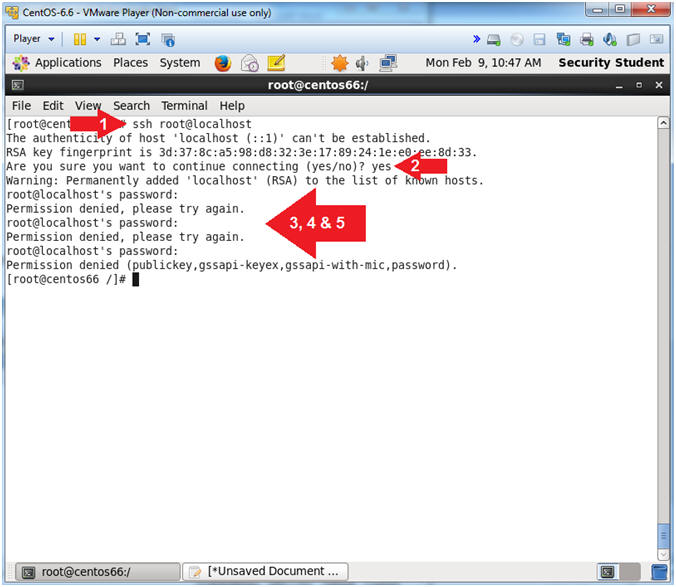
- Instructions:
| Section 9. Proof of Lab |
- Proof of Lab
- Instructions:
- ls -l /etc/ssh/sshd_config
- ls -l /etc/sysconfig/iptables
- iptables -L -n | grep ":22"
- ps -eaf | grep ssh | grep -v grep
- date
- echo "Your Name"
- Replace the string "Your Name" with your actual name.
- e.g., echo "John Gray"
-
Proof of Lab Instructions:
- Do a PrtScn
- Paste into a word document
- Upload to Moodle
-
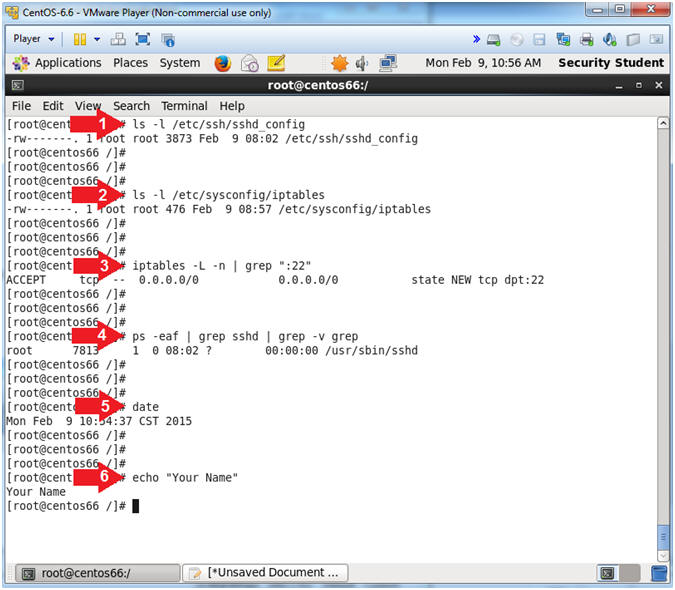
- Instructions: